Unlocking Secure Futures: The Power of AI in Data Access Management
Platform Category: Data Security & Governance Platform
Core Technology/Architecture: Machine Learning Models, Attribute-Based Access Control (ABAC), Anomaly Detection
Key Data Governance Feature: Dynamic Policy Enforcement based on user behavior and data sensitivity
Primary AI/ML Integration: Built-in ML for risk scoring, access recommendations, and threat detection
Main Competitors/Alternatives: Immuta, Privacera, Satori Cyber, Okta
AI in Data Access Management is rapidly redefining how organizations secure their most valuable asset – information. The complexities of modern data environments, where vast amounts of data reside across diverse platforms, make traditional access management approaches increasingly inadequate. This is where AI Data Access Management steps in, offering intelligent solutions to challenges once considered insurmountable by human capabilities alone, ensuring granular control and proactive threat detection across the enterprise.
Introduction: Revolutionizing Data Security with Intelligent Access
In today’s hyper-connected digital landscape, data is the new currency. Organizations across every sector are grappling with exponential data growth, stringent regulatory compliance, and an ever-evolving threat landscape. Traditional data access management systems, often reliant on static rules and manual oversight, are struggling to keep pace. The sheer volume of access requests, the dynamic nature of user roles, and the distributed architecture of data repositories (from on-premise databases to multi-cloud environments) create significant security gaps and operational inefficiencies. This critical juncture demands a paradigm shift, and AI Data Access Management emerges as the transformative solution. By leveraging advanced machine learning and artificial intelligence, these intelligent platforms automate, optimize, and fortify data access policies, moving beyond reactive security measures to a proactive, adaptive defense strategy that protects sensitive information while enabling seamless business operations. Our objective in this deep dive is to explore the intricate workings, profound benefits, inherent challenges, and comparative advantages of integrating AI into data access management frameworks.
Core Breakdown: Architecture and Capabilities of AI Data Access Management
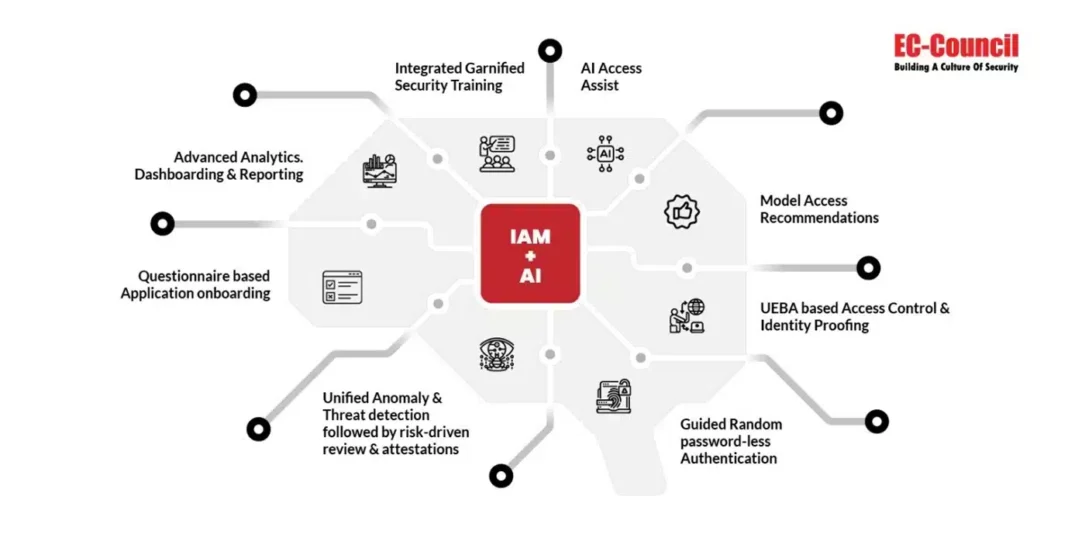
The foundation of modern data security lies in controlling who can access what data, when, and under what conditions. AI Data Access Management systems fundamentally enhance this by introducing intelligence, automation, and adaptability to an otherwise rigid process. These platforms go beyond simple role-based access control (RBAC) to offer context-aware, attribute-based access control (ABAC) fueled by machine learning.
Key Components and Mechanisms
- Contextual Access Engines: Unlike static policies, AI-powered engines analyze a multitude of real-time and historical context factors, including user identity, role, location, device, time of day, data sensitivity, and even behavioral patterns. Machine learning models continuously learn from these inputs to determine appropriate access levels.
- Attribute-Based Access Control (ABAC): At its heart, AI Data Access Management relies heavily on ABAC. AI algorithms can dynamically evaluate an extensive set of attributes associated with the user, the resource, and the environment to grant or deny access. This allows for extremely fine-grained control that scales far better than managing thousands of individual roles.
- User Behavior Analytics (UBA) and Anomaly Detection: One of the most critical AI components. Machine learning models establish baselines for normal user behavior. Any deviation from these baselines – unusual login times, access to sensitive data outside typical working hours, or attempts to download unusually large datasets – are flagged as potential anomalies. These anomalies can trigger alerts, initiate multi-factor authentication, or even temporarily revoke access until further verification. This is pivotal for insider threat detection and compromised credential mitigation.
- Automated Policy Generation and Optimization: AI can analyze existing access logs and policies to identify redundancies, inefficiencies, or potential conflicts. It can also suggest new, more optimized policies based on observed usage patterns and compliance requirements, significantly reducing the manual burden on security administrators.
- Risk Scoring and Adaptive Policies: AI models assign a risk score to each access request or user session based on the evaluated context and detected anomalies. High-risk scores can automatically trigger stricter access policies, such as requiring additional authentication steps, limiting data download capabilities, or restricting access entirely. This dynamic adaptation ensures security posture evolves with the threat landscape.
- Data Classification and Sensitivity Labeling: While often a precursor, AI plays a significant role in automating the discovery and classification of data based on its content, context, and regulatory requirements. This ensures that access policies are correctly applied to data of varying sensitivities.
Challenges and Barriers to Adoption
Despite the immense promise, integrating and fully leveraging AI in data access management comes with its own set of hurdles:
- Data Quality and Volume: AI models are only as good as the data they are trained on. Poor quality, insufficient, or biased training data can lead to ineffective policies, false positives, or, worse, security gaps. The sheer volume of access logs and contextual data required for robust training can also be challenging to collect and process.
- Complexity and Explainability: The “black box” nature of some advanced AI/ML models can make it difficult for security administrators to understand why a specific access decision was made. This lack of explainability can hinder trust, auditing, and troubleshooting, especially in highly regulated environments.
- Integration with Legacy Systems: Many organizations operate with a complex mesh of legacy systems and modern cloud applications. Integrating a sophisticated AI Data Access Management platform seamlessly across such a heterogeneous environment can be technically challenging and resource-intensive.
- Managing False Positives/Negatives: Overly aggressive anomaly detection can lead to an abundance of false positives, desensitizing security teams to actual threats. Conversely, false negatives can allow real breaches to slip through. Fine-tuning AI models to strike the right balance is a continuous effort.
- MLOps Complexity in Security: Deploying, monitoring, and maintaining machine learning models for security operations (MLOps) requires specialized skills and infrastructure. Ensuring model performance, retraining, and adaptation to new threats and data patterns is an ongoing operational challenge.
- Cost and Resource Intensity: Implementing and maintaining AI Data Access Management solutions can require significant investment in specialized software, infrastructure, and skilled personnel.

Business Value and ROI
The benefits of overcoming these challenges are substantial, translating into significant return on investment (ROI) for organizations:
- Enhanced Security Posture: AI’s ability to detect subtle anomalies and adapt policies in real-time provides a far more robust defense against both internal and external threats, significantly reducing the risk of data breaches and intellectual property theft.
- Operational Efficiency and Cost Savings: Automating access reviews, provisioning, de-provisioning, and policy enforcement dramatically reduces manual effort, freeing up IT and security teams to focus on higher-value strategic tasks. This leads to substantial cost savings and faster response times.
- Streamlined Compliance and Audit Readiness: AI-powered systems continuously monitor and enforce compliance with internal policies and external regulations (GDPR, HIPAA, CCPA, etc.). They maintain comprehensive, immutable audit trails, simplifying compliance reporting and drastically shortening audit cycles.
- Intelligent Risk Assessment: By continuously assessing user and data risk profiles, organizations can implement adaptive access policies that minimize risk without unnecessarily hindering productivity. This proactive risk management capability is invaluable.
- Improved User Experience: With automated, context-aware access, legitimate users gain faster, more seamless access to the data they need, improving productivity and reducing friction.
- Scalability for Dynamic Environments: As data volumes grow and user populations fluctuate, AI Data Access Management solutions can scale to manage complex access policies across hybrid and multi-cloud environments, ensuring consistent security without overwhelming human administrators.
Comparative Insight: AI-Powered vs. Traditional Data Access Management
To truly appreciate the transformative impact of AI Data Access Management, it’s essential to compare it with traditional approaches, which largely consist of Role-Based Access Control (RBAC) and manual policy enforcement. While foundational, traditional methods exhibit significant limitations in the face of modern data challenges.
Traditional data access management typically relies on predefined roles (e.g., “HR Manager,” “Marketing Analyst”) to which permissions are assigned. Users are then assigned to one or more roles, inheriting their associated access rights. This system, while straightforward for smaller, static environments, struggles significantly with:
- Granularity and Complexity: Achieving fine-grained access often requires creating an explosion of roles, leading to “role bloat” and an unmanageable matrix of permissions. Managing exceptions or temporary access becomes a manual, error-prone process.
- Contextual Blindness: Traditional systems are static. They don’t consider the context of an access request – whether the user is at a known secure location, using a corporate device, or exhibiting unusual behavior. An HR manager has access whether they are in the office or attempting to download sensitive payroll data from an unknown IP address at 3 AM.
- Scalability: As organizations grow, and data proliferates across diverse platforms (cloud storage, SaaS apps, on-prem databases), manually configuring and reviewing access for thousands of users and millions of data points becomes an impossible task.
- Proactive Threat Detection: Traditional systems are inherently reactive. They enforce rules but don’t actively look for anomalies or predict potential threats. Breaches are often detected long after the fact, if at all, based on external alerts or lengthy audit reviews.
- Compliance Overhead: Demonstrating compliance with dynamic regulations requires constant manual verification and auditing, which is time-consuming and prone to human error.
In contrast, AI Data Access Management transcends these limitations by injecting intelligence and dynamism into every layer:
- Dynamic, Fine-Grained Access: Instead of static roles, AI-powered systems utilize Attribute-Based Access Control (ABAC), where policies are evaluated in real-time based on a multitude of attributes (user, resource, environment). AI models dynamically assess these attributes to grant the “least privilege” access required at that exact moment.
- Context-Aware Security: AI continuously analyzes context – device posture, geo-location, time of access, historical behavior, and even the sensitivity of the data being requested – to make intelligent access decisions. If the context changes (e.g., user attempts access from an unfamiliar device), access can be automatically adjusted or revoked.
- Scalability and Automation: AI automates the discovery of data, classification, policy generation, and enforcement. This allows organizations to manage access at scale across vast, diverse data ecosystems without proportional increases in human resources. Automated user provisioning and de-provisioning are standard.
- Proactive Anomaly Detection and Threat Intelligence: Machine learning models establish baselines for normal behavior and continuously monitor for deviations. This enables real-time detection of insider threats, compromised accounts, or sophisticated external attacks, allowing for immediate remediation before significant damage occurs.
- Continuous Compliance and Audit: AI systems maintain a persistent, detailed audit trail of all access decisions, along with the contextual factors that informed them. They can automatically flag potential policy violations and generate comprehensive compliance reports, drastically simplifying audit processes and ensuring ongoing regulatory adherence.
While the upfront investment and complexity of integrating AI might seem daunting, the long-term benefits in terms of enhanced security, reduced operational overhead, superior compliance, and adaptive protection against evolving threats make AI Data Access Management an indispensable evolution for any data-driven enterprise. It transforms security from a reactive bottleneck into a proactive enabler of business agility and innovation.

World2Data Verdict: Embracing Adaptive Trust with AI Data Access Management
The future of data security is unequivocally tied to intelligence and automation. World2Data’s verdict is clear: organizations must move beyond static, perimeter-based security models and embrace the dynamic, adaptive capabilities offered by AI Data Access Management. This isn’t merely an upgrade; it’s a fundamental shift towards an “adaptive trust” framework, where access is continuously evaluated and adjusted based on real-time context and risk. We recommend that enterprises prioritize the adoption of AI-driven solutions that offer robust UBA, ABAC capabilities, and clear explainability for their ML models. Start with a pilot project in a less sensitive but representative data environment, focusing on understanding the nuances of model tuning and managing false positives. Invest in building internal expertise in MLOps for security, ensuring the continuous monitoring, retraining, and evolution of AI models to stay ahead of new threats. The ultimate goal is to achieve a state where data access is not a source of constant concern but a seamlessly managed, intelligently secured process that empowers innovation while protecting the enterprise’s most vital asset. The path to resilient and future-proof data security lies in the intelligent integration of AI into every aspect of access control.