Real-Time Data Streaming for Fraud Detection: The New Frontier in Financial Security
Platform Category: Stream Processing Engine
Core Technology/Architecture: Event-Driven Architecture
Key Data Governance Feature: Real-Time Data Quality Monitoring
Primary AI/ML Integration: Real-Time ML Model Inference
Main Competitors/Alternatives: Batch Processing Fraud Detection
The landscape of financial crime is continuously evolving, demanding increasingly sophisticated and rapid countermeasures. In this high-stakes environment, Real-Time Data Streaming for Fraud Detection has emerged as a critical capability, transforming how organizations combat illicit activities. By processing and analyzing transactional data the moment it is generated, businesses can identify and neutralize fraudulent patterns instantaneously, drastically minimizing potential losses and safeguarding customer trust. This immediate responsiveness empowers enterprises to maintain financial integrity and secure their operations against the most advanced threats.
The New Imperative: Why Real-Time Fraud Detection Streaming is Non-Negotiable
Traditional fraud detection methods, predominantly reliant on batch processing, are fundamentally ill-equipped for the demands of the modern digital economy. The inherent delays in these systems—often hours or even days between a fraudulent event and its detection—create vast windows of opportunity for sophisticated criminals to exploit, leading to significant financial losses and reputational damage. In a world where billions of transactions occur daily across diverse channels, the ability to act within milliseconds is not merely an advantage but an absolute necessity. Real-Time Fraud Detection Streaming addresses this critical gap, providing the immediate insights required to respond to anomalous patterns with unprecedented speed and precision, thereby ensuring the integrity and security of every single transaction before it’s too late.
The shift towards real-time capabilities is driven by several factors. Firstly, the sheer volume and velocity of data generated by digital interactions necessitate continuous processing. Legacy systems struggle to cope with the influx of high-speed, unstructured, and semi-structured data from diverse sources like mobile apps, IoT devices, and online platforms. Secondly, customer expectations for seamless and secure transactions are higher than ever, making any compromise in security or service intolerable. A delay in detecting fraud can lead to prolonged customer service issues, account freezes, and ultimately, a loss of confidence. Thirdly, the sophistication of fraud schemes has escalated dramatically, with fraudsters leveraging advanced techniques such as synthetic identities, account takeovers, and bot attacks that demand equally advanced, adaptive, and immediate detection mechanisms. Organizations that fail to adopt Real-Time Fraud Detection Streaming risk not only monetary losses but also erosion of customer confidence, potential regulatory penalties, and a damaged brand reputation. Speed, therefore, is no longer just a metric; it is a core competitive advantage and a fundamental pillar of modern risk management, enabling proactive defense rather than reactive damage control.
Core Breakdown: Architecture and Technologies Powering Real-Time Fraud Detection
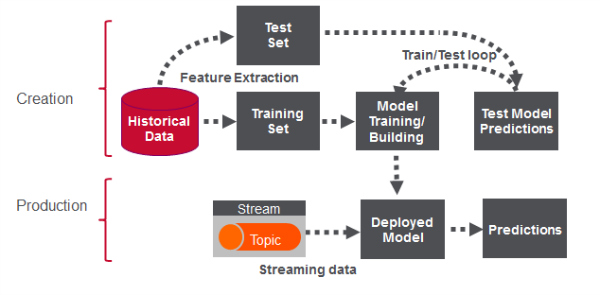
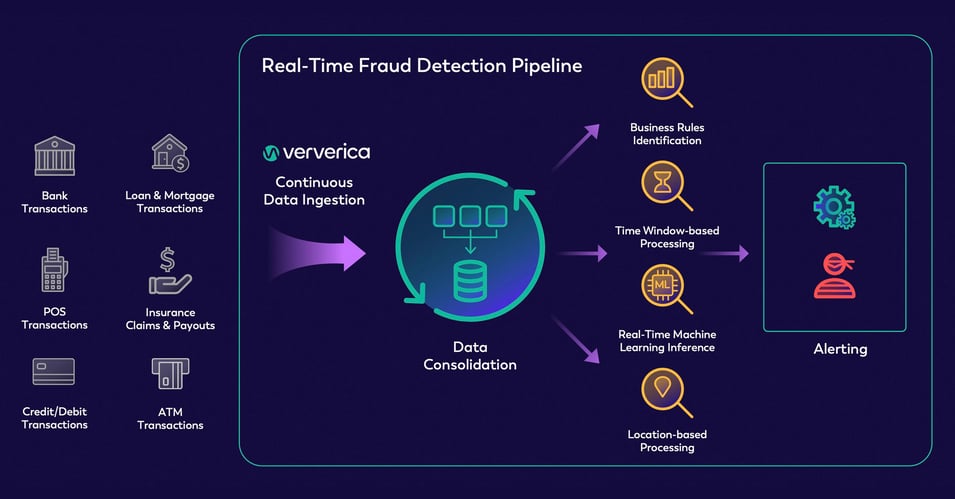
The foundation of effective Real-Time Data Streaming for Fraud Detection lies in a robust, event-driven architecture capable of ingesting, processing, and analyzing vast quantities of data the instant it is generated. This architecture moves beyond static data stores, focusing instead on continuous data flow and immediate action. At its heart, it comprises several key components working in concert, forming a dynamic pipeline for threat intelligence:
Data Ingestion and Stream Processing
- Event Sources: Data originates from a multitude of sources, each representing a potential point of fraud or legitimate activity. These include payment gateways (credit card transactions, ACH transfers, wire transfers), online banking activities, user login attempts, device information (IP address, device ID, browser fingerprint), geolocation data, e-commerce interactions (shopping cart behavior, product views), and even social media signals or public record data. Each interaction is treated as an immutable “event” that must be captured and processed.
- Message Queues/Brokers: Technologies like Apache Kafka, Amazon Kinesis, or Google Cloud Pub/Sub are central to this stage. They act as highly scalable, fault-tolerant, distributed conduits that buffer and distribute streams of events. This ensures reliable data delivery, preserves event order, and decouples producers from consumers, allowing for asynchronous processing and exceptionally high throughput. Message brokers are crucial for handling peak loads and ensuring data is never lost, even if downstream systems are temporarily unavailable.
- Stream Processing Engines: Once ingested, raw event data is fed into powerful stream processing engines such as Apache Flink, Apache Spark Streaming, or Google Cloud Dataflow. These engines are designed to perform real-time computations on data in motion, enabling complex operations within milliseconds. They can perform real-time aggregations (e.g., total spend from a user in the last 5 minutes), apply windowing functions (e.g., counting login attempts within a sliding 60-second window), execute joins across multiple data streams (e.g., joining transaction data with user profile data), and perform complex event processing (CEP) to identify intricate sequences of events indicative of fraud. These engines are the computational backbone, transforming raw events into actionable insights on the fly.
Advanced Analytics and Machine Learning Integration
- Feature Engineering (Real-Time): Critical to effective fraud detection is the ability to derive meaningful features from raw event streams. This involves creating various types of features instantaneously:
- Aggregations: Calculating statistics over a defined window, such as the number of transactions, total amount spent, or unique merchants visited from a specific IP address in the last hour.
- Velocity Features: Detecting rapid changes in behavior, like an unusually high number of login attempts, credit card transactions, or password resets within a short timeframe compared to historical norms.
- Contextual Features: Enriching events with external data, such as a customer’s historical spending patterns, geographic risk scores, or known fraudulent IP addresses from a blacklist, often retrieved from low-latency databases or in-memory caches.
These features are often computed directly within the stream processing engine or through a dedicated feature store designed for real-time access.
- Machine Learning Models: Pre-trained machine learning models are deployed to consume these real-time features and make instantaneous predictions. These models are the intelligence layer, constantly learning from new data to identify evolving fraud patterns. Common model types include:
- Anomaly Detection Models: These models identify transactions or behaviors that deviate significantly from established normal patterns, without necessarily being trained on labeled fraud data. Techniques like Isolation Forests, One-Class SVMs, or autoencoders are frequently used to spot the unusual.
- Supervised Learning Models: Trained on vast historical labeled data (fraudulent vs. legitimate transactions), these models (e.g., Gradient Boosting Machines, XGBoost, Logistic Regression, Deep Neural Networks) classify incoming transactions in real time as high or low risk of fraud. They learn the intricate patterns that differentiate legitimate from illicit activities.
- Graph Neural Networks (GNNs): Increasingly, graph databases and GNNs are used to detect complex fraud rings by analyzing relationships between entities (users, devices, accounts, transactions) in real-time, identifying suspicious clusters, cycles, or paths that indicate collusion or coordinated attacks.
- Rule Engines: Complementing ML models, sophisticated rule engines allow subject matter experts to define specific, business-driven rules (e.g., “block any transaction over $1000 from a new device in a high-risk country if the user’s login location is inconsistent”). These rules provide a crucial layer of explainability, compliance, and deterministic control, often acting as a first line of defense or a final arbiter for high-certainty cases where human expertise is codified.
Action and Feedback Loop
- Real-Time Decisioning: Based on the combined output of ML models and rule engines, the system makes an immediate decision: approve, deny, flag for manual review, or request additional verification (e.g., Two-Factor Authentication, biometric check). This decision can trigger automated actions within the payment system, customer communication channels, or internal alert systems, all within the critical response window.
- Feedback Loop: A continuous feedback loop is vital for maintaining the efficacy of a real-time fraud detection system. Outcomes of decisions (e.g., a flagged transaction later confirmed as fraud, or a blocked transaction subsequently confirmed as legitimate) are fed back into the system. This data is used to retrain and fine-tune ML models, update rule sets, and improve feature engineering, ensuring they remain accurate, adaptive, and resilient to new and evolving fraud patterns. This continuous learning is a hallmark of a mature, intelligent Real-Time Fraud Detection Streaming system.
Challenges and Barriers to Adoption
While the benefits of Real-Time Data Streaming for Fraud Detection are clear and compelling, implementing such a system is not without its significant challenges, requiring careful planning and substantial investment:
- Data Volume and Velocity: Managing petabytes of diverse data flowing at incredibly high speeds (often millions of events per second) requires significant infrastructure, distributed computing expertise, and sophisticated engineering talent. Scaling these systems efficiently and cost-effectively can be a major hurdle.
- Data Quality and Consistency: Real-time data streams often originate from disparate and heterogeneous sources, leading to inconsistencies, missing values, incorrect formatting, or erroneous data. Ensuring high data quality, integrity, and consistency in real-time is paramount for accurate fraud detection, as “garbage in, garbage out” applies acutely here. Robust Real-Time Data Quality Monitoring is essential to catch and mitigate issues instantly.
- Model Drift and Explainability: Fraud patterns constantly evolve; fraudsters adapt their tactics, leading to model drift where pre-trained models become less effective over time. Continuous monitoring, A/B testing, and frequent retraining (often using MLOps principles) are necessary to maintain model performance. Furthermore, explaining why a specific transaction was flagged (explainable AI) is crucial for compliance, customer service interactions, and regulatory audits, especially in sensitive financial contexts.
- Integration Complexity: Integrating stream processing platforms, diverse machine learning services, complex rule engines, and existing operational systems (like core banking platforms, payment gateways, CRM systems) can be incredibly complex, time-consuming, and resource-intensive, requiring careful orchestration and API development.
- False Positives: Overly aggressive detection rules or models can lead to legitimate transactions being erroneously blocked, causing significant customer frustration, potential churn, and lost revenue. Balancing detection accuracy with minimizing false positives (and false negatives, which represent missed fraud) is a continuous and delicate challenge that impacts both security and user experience.
- Latency Requirements: Meeting strict latency Service Level Agreements (SLAs) for real-time decisions (often sub-100 milliseconds) requires highly optimized infrastructure, efficient algorithms, and careful network design, pushing the boundaries of system performance.
- Cost of Infrastructure and Talent: Building and maintaining a high-performance, fault-tolerant, and scalable real-time streaming architecture can be costly, requiring significant investment in cloud computing resources, specialized hardware, and highly skilled data engineers, machine learning engineers, and data scientists.
- Security and Privacy: Handling sensitive financial and personal data in real-time streams demands stringent security measures, including encryption, access controls, and compliance with data privacy regulations (e.g., GDPR, CCPA).
Business Value and ROI of Real-Time Fraud Detection Streaming
Despite the inherent challenges, the return on investment (ROI) for a well-implemented Real-Time Data Streaming for Fraud Detection system is substantial, driving significant and measurable business value across multiple dimensions:
- Minimized Financial Losses: The most direct and tangible benefit is the prevention of fraudulent transactions before they complete. By blocking fraud in real-time, organizations prevent chargebacks, eliminate the costs associated with investigating and resolving fraud cases, and directly protect their revenue streams. This proactive approach significantly reduces the “cost of fraud.”
- Enhanced Customer Trust and Experience: Customers inherently appreciate the security of knowing their transactions are constantly monitored and protected. Real-time detection minimizes the impact of fraud on customers, reducing the inconvenience of stolen funds, compromised accounts, or identity theft, thereby building stronger loyalty and improving overall customer satisfaction. A seamless and secure experience is a powerful differentiator.
- Improved Operational Efficiency: Automated real-time decisions reduce the need for manual review of suspicious transactions, significantly lowering the workload on fraud analysts. This allows fraud teams to shift from reactive firefighting to focusing on more complex cases, strategic intelligence, model optimization, and proactive threat hunting, leading to better resource allocation and higher job satisfaction.
- Regulatory Compliance: Many industries, especially finance, face stringent regulations regarding fraud prevention and reporting (e.g., Anti-Money Laundering (AML), Payment Services Directive 2 (PSD2), Know Your Customer (KYC)). Real-time systems help organizations meet these compliance obligations more effectively by providing auditable trails, immediate anomaly detection, and robust reporting capabilities, mitigating the risk of hefty fines and legal repercussions.
- Adaptability to Evolving Threats: With continuous learning capabilities embedded in the real-time ML pipeline, these systems can adapt quickly to new fraud typologies, emerging patterns, and sophisticated attack vectors. This allows organizations to stay ahead of criminals rather than reacting after damage has been done, fostering a truly proactive security posture.
- Competitive Advantage: Companies that offer superior fraud protection and a frictionless, secure transaction experience can differentiate themselves significantly in the market. This attracts and retains more customers who prioritize security and reliability, reinforcing brand reputation and market share.
- Better Resource Utilization: Real-time systems can optimize resource usage by intelligently routing transactions. For instance, low-risk transactions can proceed without delay, while only truly suspicious ones are flagged for further scrutiny, leading to more efficient processing.
Comparative Insight: Real-Time Data Streaming vs. Traditional Fraud Detection
Understanding the paradigm shift introduced by Real-Time Data Streaming for Fraud Detection requires a direct comparison with traditional approaches, which primarily relied on batch processing over historical data. This comparison highlights not just technological differences but fundamental shifts in strategy, capability, and the very nature of fraud prevention:
Traditional Fraud Detection (Batch Processing)
- Data Latency: Data is collected over a significant period (typically hours or days), batched into large datasets, and then processed during off-peak hours. Fraud detection is inherently retrospective, occurring long after the fraudulent event has transpired. This lag is the system’s biggest vulnerability.
- Data Sources: Typically relies on structured data from relational databases, data warehouses, and potentially data lakes. Data is often cleaned, transformed, and aggregated before analysis, losing granularity in the process.
- Analysis Methodology: Focuses on historical analysis, periodic reporting, and scheduled model runs. Models are often trained on static datasets and deployed periodically (e.g., monthly or quarterly). Detection is based on rules and statistical models applied to aggregated, historical snapshots of data.
- Actionability: Actions are almost entirely reactive. Once fraud is detected, the focus shifts to recovery of funds (often difficult), investigation (resource-intensive), and preventing future occurrences through rule updates. The initial fraudulent transaction often goes through successfully, leading to direct financial losses, chargebacks, and significant customer impact.
- System Architecture: Characterized by traditional ETL (Extract, Transform, Load) pipelines that move data from operational systems into a central data warehouse for analysis. These architectures are designed for stability and reporting, not speed.
- Use Cases: Ideal for identifying long-term trends, generating periodic compliance reports, and deep post-event forensic analysis. Less effective, or entirely ineffective, for immediate threat mitigation and real-time intervention.
Real-Time Data Streaming for Fraud Detection
- Data Latency: Processes data as it arrives, with detection happening in milliseconds (often sub-100ms). This enables proactive intervention—blocking or challenging transactions before they are completed, preventing damage rather than just reacting to it.
- Data Sources: Ingests continuous streams of raw, granular data from diverse operational systems, API gateways, IoT devices, web logs, mobile apps, and payment processing platforms. Data is treated as an endless flow of events.
- Analysis Methodology: Employs powerful stream processing engines and real-time machine learning models to analyze data in motion. Features are engineered on the fly, and ML models infer risk scores instantaneously. Complex rule engines operate directly on live events, allowing for dynamic adaptation.
- Actionability: Actions are proactive and immediate. Fraudulent transactions can be blocked, subjected to additional real-time verification (e.g., biometric challenge), or immediately flagged for human review within the transaction window, preventing financial losses and protecting the customer experience from the outset.
- System Architecture: Built on event-driven principles, utilizing robust message brokers (e.g., Apache Kafka) and high-performance stream processing frameworks (e.g., Apache Flink, Apache Spark Streaming). Often integrates with real-time databases and in-memory caches for rapid contextual lookups and state management.
- Use Cases: Essential for preventing financial losses in high-volume, high-velocity environments, protecting customer accounts from immediate threats, ensuring continuous regulatory compliance, and maintaining a real-time, adaptive security posture against dynamic fraud.
The fundamental difference lies in timing and impact. Traditional systems are akin to looking at a security camera recording after a crime has occurred, allowing for investigation but not prevention. Real-Time Data Streaming for Fraud Detection is like having a security guard who can intercept a suspicious person mid-act, preventing the crime before it inflicts harm. While traditional systems provide valuable insights into past fraud patterns for strategic improvements, real-time systems actively prevent future fraud, turning data from a historical record into a live, actionable defense mechanism. The most effective contemporary fraud prevention strategies often involve hybrid approaches, leveraging the best of both worlds—real-time for immediate prevention and batch for deeper analytical insights, comprehensive reporting, and robust model retraining cycles.

World2Data Verdict: The Future is Now for Fraud Prevention
The imperative for real-time capabilities in fraud prevention is no longer a futuristic vision; it is a present-day reality and a strategic necessity for any organization operating in the digital realm. The relentless pace of digital transactions, combined with the escalating sophistication and speed of financial fraud schemes, demands a proactive, instantaneous defense mechanism. Investing in robust Real-Time Data Streaming for Fraud Detection infrastructure is not merely an IT upgrade but a fundamental shift in business strategy, providing unparalleled resilience against evolving threats and directly impacting profitability, operational efficiency, and customer loyalty. Organizations that embrace this transformation will not only protect their assets more effectively and comply with stringent regulations, but will also build a stronger foundation of trust with their customers, positioning themselves as leaders in secure digital commerce. The future of fraud prevention is dynamic, intelligent, and unequivocally real-time, requiring continuous adaptation, advanced analytical capabilities, and unwavering innovation.