Security Monitoring Analytics: A Deep Dive into Proactive Threat Detection
Security Monitoring Analytics: A Case Study on Threat Detection highlights the critical role modern organizations face in safeguarding their digital assets against an ever-evolving cyber threat landscape. Traditional, static defenses are often insufficient, necessitating a more dynamic and intelligent approach. Robust security monitoring analytics offers a proactive shield, transforming vast quantities of raw security data into actionable intelligence, enabling organizations to anticipate, detect, and respond to threats with unprecedented speed and precision.
The Imperative of Modern Security Monitoring Analytics
Understanding the imperative of Security Monitoring Analytics is paramount in today’s interconnected digital age. As organizations embrace digital transformation, cloud computing, and remote work, their attack surface expands dramatically, making them vulnerable to sophisticated and persistent cyberattacks. The sheer volume, velocity, and variety of security events generated across an enterprise environment demand more than simple log aggregation or rule-based alerts. Organizations must move beyond reactive measures, adopting comprehensive security monitoring analytics to predict and prevent breaches before they escalate into catastrophic events. This shift from post-mortem analysis to real-time, predictive threat detection is not merely an operational upgrade; it’s a strategic necessity for maintaining business continuity, protecting sensitive data, and preserving customer trust. Modern analytics platforms leverage advanced computational power to sift through noise, identify subtle anomalies, and correlate seemingly unrelated events to expose sophisticated attack campaigns that would otherwise go unnoticed by human operators or legacy systems.
Core Breakdown: Architecture, Components, and the Power of Proactive Threat Detection
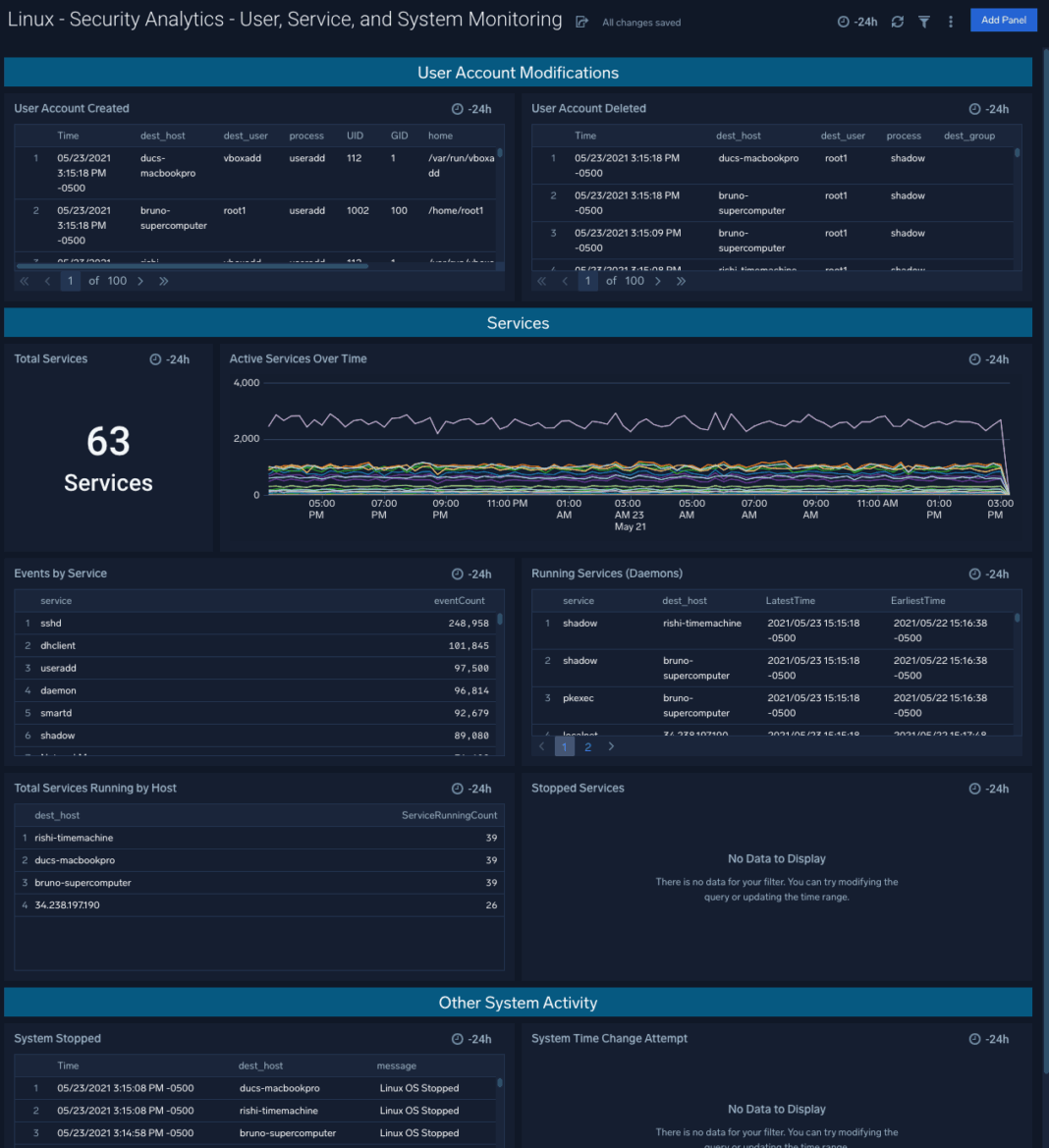
Effective Security Monitoring Analytics involves a multi-layered, integrated strategy, built upon a sophisticated architecture designed for scale and intelligence. This approach goes far beyond traditional SIEM (Security Information and Event Management) systems by incorporating advanced analytics and machine learning capabilities to offer a holistic view of an organization’s security posture.
Key Architectural Components and Technologies:
- Big Data Processing & Real-time Stream Analytics: At its foundation, an effective platform must be able to ingest, process, and store massive volumes of diverse data from endpoints, network devices, applications, cloud environments, identity systems, and threat intelligence feeds. This necessitates robust big data processing capabilities, often leveraging cloud-native architectures for scalability, coupled with real-time stream analytics to identify malicious activities as they occur, minimizing the window of compromise.
- Behavioral Analytics (UEBA): User and Entity Behavior Analytics (UEBA) is a cornerstone of modern security analytics. It establishes dynamic baselines of normal behavior for users, devices, and applications across the network. Any significant deviation from these baselines, such as unusual login attempts from rarely used geographic locations, access to sensitive data outside working hours, or atypical data transfer volumes, is flagged as a potential threat. This allows for the detection of insider threats, compromised accounts, and novel attack techniques that signature-based methods would inevitably miss.
- Correlation Engines: These sophisticated engines are crucial for connecting disparate security events across the entire digital infrastructure. They analyze thousands of events per second, identifying complex patterns and relationships that indicate a larger, coordinated attack. For instance, a failed login from one country, followed by a successful login from another, and then unusual access to a critical server, might individually be low-priority, but together form a high-fidelity alert.
- Threat Intelligence Integration: Incorporating external threat intelligence feeds provides crucial context and predictive power. This includes known malicious IP addresses, command-and-control (C2) domains, malware hashes, and indicators of compromise (IoCs) associated with specific threat actors and campaigns. Integrating this intelligence allows the platform to enrich internal alerts, proactively block known threats, and prioritize threats more effectively.
- Machine Learning for Pattern Recognition & Anomaly Detection: AI and ML are fundamental to the operational efficiency of modern platforms. They automate the identification of complex attack patterns, predict potential threats, and significantly reduce false positives. Machine learning models can be trained to recognize new attack vectors, automatically score the severity of threats based on multiple contextual factors, and even suggest remediation actions, aiding analysts in focusing on the most critical issues.
- Cloud-native Architectures: Many leading security analytics platforms are built on cloud-native foundations, leveraging microservices, containers, and serverless computing. This provides unparalleled scalability, resilience, global reach, and cost-efficiency, allowing organizations to adapt to rapidly changing data volumes and security requirements without extensive on-premise infrastructure.
A Practical Case Study in Threat Detection:
Consider a multinational corporation utilizing an advanced security monitoring analytics platform. Their system continuously collects logs from thousands of endpoints, network devices, cloud services, and identity providers globally.
One evening, the platform detects a series of unusual events that, when correlated, reveal a sophisticated attack:
- An employee account, typically active only from the corporate office in London, registers a successful login from an IP address in a country not associated with the company’s operations (e.g., Vietnam). This is an immediate flag by the UEBA component, which identifies it as an anomalous location and time of access.
- Shortly after this login, the same account attempts to access a highly sensitive financial database, something it has never done before, especially not outside business hours. Behavioral analytics registers this as a severe anomaly, indicating privilege escalation or misuse.
- Concurrently, the system identifies a large volume of data being exfiltrated from the financial database to an external, unapproved cloud storage service. The platform’s machine learning models have previously identified this pattern as indicative of data theft or espionage.
- Further analysis by the correlation engine reveals that the external IP address for the data exfiltration matches a known indicator of compromise (IoC) from a recent threat intelligence feed, linking it to a state-sponsored APT (Advanced Persistent Threat) group.
Individually, each event might seem minor or even be explained away. However, the security monitoring analytics platform’s correlation engine, powered by real-time stream analytics and AI, connects these dots instantly. It flags the entire sequence as a high-priority incident: “Potential Data Exfiltration via Compromised User Account Linked to APT.” The platform automatically triggers an alert, enriches it with contextual information (user role, asset criticality, threat intelligence on the destination IP), and initiates an automated response playbook, such as isolating the affected endpoint, temporarily suspending the compromised user account, and alerting the security operations center (SOC) for immediate human intervention. This comprehensive, rapid view helps pinpoint complex, multi-stage attacks that might otherwise remain undetected for extended periods, preventing significant data loss and reputational damage.
Challenges and Barriers to Adoption:
Despite the clear benefits, implementing and optimizing security monitoring analytics platforms comes with its own set of challenges that organizations must carefully navigate:
- Alert Fatigue: Without proper tuning, robust filtering, and advanced AI/ML capabilities, the sheer volume of alerts generated by a comprehensive monitoring system can overwhelm security teams, leading to ignored critical alerts and burnout.
- Data Volume and Complexity: Managing, storing, and analyzing petabytes of diverse log data from a multitude of sources (endpoints, cloud, network, applications) requires significant infrastructure, specialized tools, and expertise. Data quality, normalization, and contextualization are also crucial and often challenging.
- Skill Gap: There’s a persistent global shortage of security analysts with the necessary skills in data science, machine learning, and advanced analytics to fully leverage these sophisticated platforms. Training and retaining such talent is a significant barrier.
- Integration Complexity: Integrating disparate security tools, legacy systems, and dynamic cloud environments into a unified analytics platform can be technically challenging, time-consuming, and require significant customization efforts.
- Cost: The initial investment in software licenses, hardware, professional services, and ongoing operational costs (data storage, compute, maintenance, staff training) can be substantial, making ROI justification a critical factor.
- Data Governance & Privacy: Processing vast amounts of sensitive log data necessitates robust data governance features. This includes strict Role-Based Access Control (RBAC) to limit who can access certain logs, stringent data retention policies to meet legal requirements, comprehensive audit trails for accountability, and data masking/anonymization for sensitive logs to ensure compliance with evolving regulations like GDPR, CCPA, and HIPAA.
Business Value and ROI:
The business impact of robust Security Monitoring Analytics is profound and far-reaching, extending beyond just technical security. It delivers tangible return on investment across multiple organizational facets:
- Mitigated Financial & Reputational Damage: By preventing or rapidly containing breaches, organizations avoid the enormous direct costs associated with data recovery, regulatory fines, legal fees, customer churn, and the long-term, often irreversible damage to brand reputation and market trust.
- Enhanced Compliance & Audit Readiness: These platforms significantly facilitate adherence to various regulatory mandates (e.g., PCI DSS, ISO 27001, SOC 2, HIPAA) by providing comprehensive audit trails, granular reporting capabilities, and demonstrable proof of security controls, simplifying compliance audits.
- Improved Operational Efficiency: Automation and orchestration benefits streamline security operations, reducing manual effort, freeing up highly skilled security analysts to focus on strategic threat hunting and proactive risk management rather than sifting through endless logs, and enabling faster, more efficient incident response.
- Continuous Business Operations: By minimizing downtime caused by cyberattacks, ransomware, or data breaches, these platforms play a critical role in ensuring business continuity, maintaining productivity, and safeguarding revenue streams.
- Proactive Risk Reduction: Beyond reactive incident response, the predictive capabilities of advanced analytics allow organizations to identify and address vulnerabilities, misconfigurations, and emerging threat patterns before they are exploited. This shifts security left, strengthening the overall security posture and reducing the organization’s attack surface.

Comparative Insight: Modern Security Monitoring Analytics vs. Traditional Approaches
The evolution of security monitoring analytics represents a paradigm shift from traditional cybersecurity frameworks. Historically, security operations relied heavily on signature-based Intrusion Detection Systems (IDS), basic firewalls, antivirus software, and first-generation SIEM (Security Information and Event Management) systems. While these tools remain foundational components of a layered defense, they often suffer from several limitations when confronted with the speed, sophistication, and volume of modern cyber threats.
Traditional SIEMs, for instance, excel at log aggregation, basic correlation based on predefined rules, and compliance reporting. They are effective at detecting known threats and policy violations for which clear rules or signatures exist. However, they typically struggle with:
- Unknown Threats (Zero-Days): Rule-based systems cannot detect threats for which no signature or rule has been explicitly defined, leaving organizations vulnerable to novel attack vectors.
- Low and Slow Attacks: Sophisticated attackers often operate subtly, making small, seemingly innocuous changes over extended periods that easily evade simple threshold alerts or rule-based detections.
- Contextual Blindness: Without advanced analytics, traditional SIEMs often lack the context to understand the broader implications or true severity of an alert, leading to a high volume of false positives and subsequent alert fatigue among security analysts.
- Scalability for Big Data: Legacy SIEM architectures may struggle to efficiently ingest, process, and analyze the petabytes of diverse data generated by modern, distributed IT environments, especially dynamic cloud-native applications and IoT devices.
- Limited Behavioral Analysis: Traditional systems often lack the capability to profile user and entity behavior, making it difficult to detect insider threats or compromised accounts that use legitimate credentials.
In contrast, modern security monitoring analytics platforms, often categorized as Security Analytics Platforms, Next-Generation SIEMs, or Extended Detection and Response (XDR) solutions, overcome these limitations through several key advancements:
- Behavioral Intelligence: Moving beyond signatures, these platforms establish dynamic baselines of normal behavior using advanced AI/ML and UEBA, enabling the detection of anomalies that signal new, unknown, or insider threats. This is a core strength for identifying threats without relying on prior knowledge of their signatures.
- Holistic Visibility & XDR: XDR platforms extend beyond traditional endpoint and network visibility to integrate data from cloud workloads, email, identity, SaaS applications, and more. This provides a unified, contextualized view of an attack across the entire digital estate, enabling more comprehensive threat detection and rapid investigation and response.
- Predictive & Proactive Capabilities: Leveraging machine learning, deep learning, and historical data, these platforms can identify emerging threat patterns, predict potential attack vectors, and even help in proactive threat hunting, shifting from reactive defense to preventive security.
- Automated Response & Orchestration: Modern platforms often integrate with Security Orchestration, Automation, and Response (SOAR) capabilities, allowing for automated responses to validated threats, such as isolating compromised devices, blocking malicious IPs, enforcing new access policies, or triggering alerts in incident management systems, thereby reducing mean time to response (MTTR).
- Cloud-Native Scalability: Built on cloud-native architectures, these solutions offer elastic scalability, superior resilience, cost-effectiveness, and global reach, making them ideal for dynamic enterprise environments with ever-increasing data volumes.
- Enhanced Threat Intelligence: Deeper integration and automated utilization of external threat intelligence feeds enrich internal data, allowing for more accurate and faster identification of malicious activities linked to known adversaries.
The transition from traditional, siloed security tools to integrated, analytics-driven platforms signifies a critical evolution in cybersecurity. It empowers organizations to move from simply reacting to known threats to proactively anticipating and neutralizing complex, unknown threats, providing a far more resilient and adaptive security posture in the face of an increasingly aggressive threat landscape.

World2Data Verdict: Pioneering Proactive Defense with Advanced Analytics
The landscape of cyber threats is evolving at an unprecedented pace, rendering reactive security measures increasingly ineffective and unsustainable. The World2Data verdict is clear: investing in robust and intelligent security monitoring analytics is no longer an optional expenditure but a strategic imperative for any organization aiming to safeguard its digital future. The power to transform raw, disparate security logs into actionable, real-time intelligence through advanced AI, machine learning, and behavioral analytics provides an unparalleled advantage in detecting and neutralizing sophisticated threats before they inflict significant financial and reputational damage.
Organizations must prioritize solutions that offer comprehensive data ingestion, intelligent correlation, contextual enrichment, and automated response capabilities, moving beyond traditional SIEMs to embrace next-generation security analytics platforms and XDR solutions. While challenges such as alert fatigue, managing data volume, and the persistent skill gap exist, the long-term ROI in terms of breach prevention, enhanced compliance assurance, and significantly improved operational efficiency far outweighs the initial investment. The future of cybersecurity unequivocally belongs to those who leverage data intelligently to predict, prevent, and respond with agility and precision. World2Data recommends a phased, strategic approach to adoption, focusing on identifying critical data sources, establishing clear use cases aligned with business risk, continuously refining the platform’s intelligence through feedback loops, and deeply integrating external threat intelligence. Embrace advanced security monitoring analytics not just as a tool, but as the cornerstone of a resilient, proactive cybersecurity strategy that effectively protects your most valuable assets in the digital age.